Collibra Console SSO configuration
You can access Collibra Console with user accounts that are created within Collibra Console. Besides those user accounts, you can also configure single sign-on (SSO) access to enable integration with your SSO infrastructure.
Tip If you want to use a custom certificate in the SSO configuration for Collibra Console access, see this section.
Prerequisites
- Your identity provider (IDP) supports SAML 2.0.
Steps
- Open Collibra Console with a user profile that has at least the ADMIN role.
Collibra Console opens with the Infrastructure page.
- In the main menu, click Console settings.
- In the tab bar, click Configuration.
- In the middle column, click Security Configuration.
- Click Edit configuration.
- Enter the required information:
Setting Description Mode The SSO mode of Collibra Console. Collibra Console only supports SAML_ATTRIBUTES.
When SSO is enabled, a user can still navigate to the /signin page and try to log in via that page. However, you can disable that page.
 True: Users cannot access the Collibra Console signin page.
True: Users cannot access the Collibra Console signin page. False (default): Users can access the Collibra Console signin page
False (default): Users can access the Collibra Console signin page
Default role
The default role for all SSO users. The default role is READ.
SSO users with a SUPER role will be downgraded to users with the ADMIN role. Only a Collibra Console SUPER user can enable the SUPER role for SSO users.
Enable SSO SUPER users(**)
 True: SSO users can have the SUPER role.
True: SSO users can have the SUPER role. False (default): SSO users with the SUPER role will be downgraded to users with the ADMIN role.
False (default): SSO users with the SUPER role will be downgraded to users with the ADMIN role.
This option is only visible if you have the SUPER role.
SAML The configuration of SAML. Metadata HTTP The URL of the SAML metadata file to be used. The URL always has to be reachable by the Collibra environment. Entity ID The entity ID inside the metadata to be referenced.
Note A metadata file can describe multiple entity IDs, make sure to use in the entity ID from the correct metadata file.
Consumer service URL By default, this URL is the same as the URL of your Collibra environment but if your IDP expects another value, you can fill it out here.
Warning Make sure that the intended destination endpoint (The Destination attribute in the SAML response) matches the URL being used here. So this is only to be used in specific IDP circumstances When setting this, and getting the error "SAML message intended destination endpoint did not match recipient endpoint" check the Destination attribute in your SAML response and this parameter.
Disable client address  True: The validation of the client IP address in the assertion message is disabled.
True: The validation of the client IP address in the assertion message is disabled. False (default): The validation of the client IP address in the assertion message is enabled.
False (default): The validation of the client IP address in the assertion message is enabled.
Sign authentication requests (Requires restart)  True: Authentication requests have to be signed. Use a Collibra generated self-signed certificate to sign requests. The request that is generated by Collibra Console will be appended with a signature in the redirect URL of the response.
True: Authentication requests have to be signed. Use a Collibra generated self-signed certificate to sign requests. The request that is generated by Collibra Console will be appended with a signature in the redirect URL of the response. False (default): Authentication request don't have to be signed.
False (default): Authentication request don't have to be signed.
Force authn  True (default): The SP authentication request forces re-authentication.
True (default): The SP authentication request forces re-authentication. False: The SP authentication request does not force re-authentication.
False: The SP authentication request does not force re-authentication.
Force passive Configure whether the SP authentication should set the authentication to go passive.
If True, the IDP or browser MUST NOT take visibly control of the user interface. See the SAML 2.0 specification for more details.
This is only relevant if Force authn is True.
Name ID Configure the nameID used in the SP authentication. If set, the full content will be sent as a nameID. Use a fully qualified nameID.
Default nameID="urn:oasis:names:tc:SAML:2.0:nameid-format:persistent". See SAML 2.0 specification for accepted nameID values.
Group to Role mapping Map groups from the group field to a role in the Collibra Console. The Field key must be a name of a group as defined in your IDP, the Field value is one of the Collibra Console roles (READ, ADMIN, SUPER). Attribute fields The mappings of attributes in the SAML response. The values are used as keys to look for in the SAML response. Username The mapping for the user's username. The value of this attribute must be the name of the SAML attribute as defined in your IDP.
In the following example, the value in Collibra Console must be email. This is the used name in your IDP software, see the following screenshot.
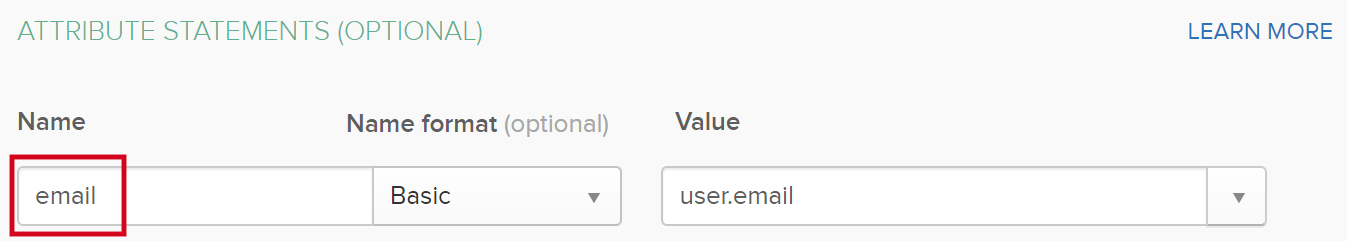
This field is mandatory.
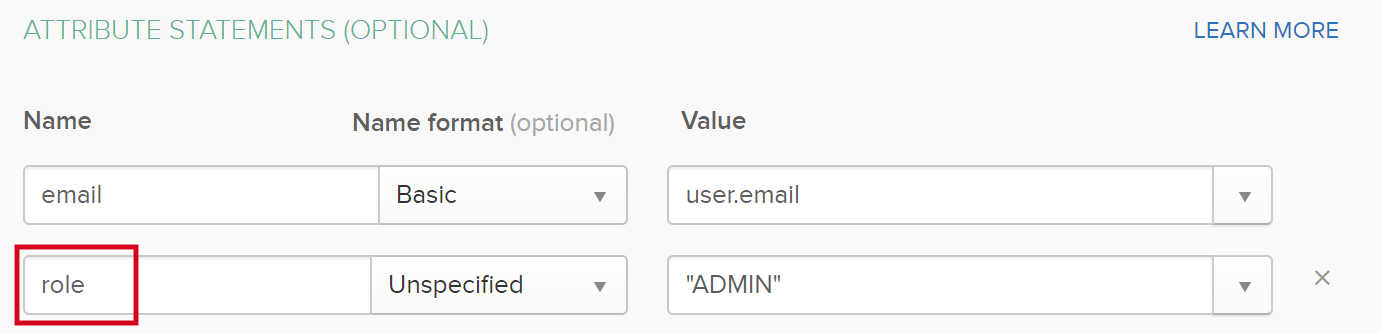
Role The mapping for the user roles. The value of this attribute must be the name of the SAML attribute as defined in your IDP.
In the following example, the value in Collibra Console must be role. This is the used name in your IDP software, see the following screenshot.
Group The mapping to define which attribute holds group information. The value of this attribute must be the name of the SAML attribute as defined in your IDP.
In the following example, the value in Collibra Console must be groups. This is the used name in your IDP software, see the following screenshot.
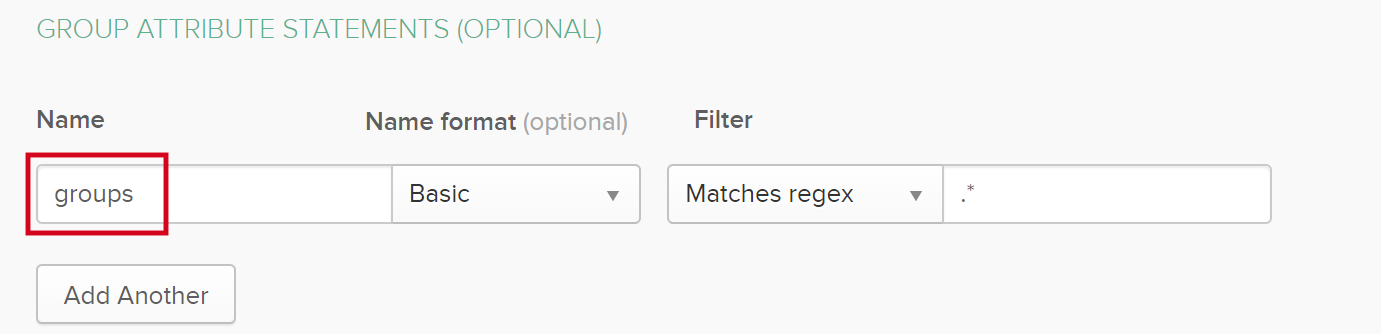
If there is more than one group attribute statement, add them as comma-separated list.
SAML Requested authentication context Settings for the SAML requested authentication context. The authentication context is the way in which the IDP authenticates the user. By default the authentication context will mandate user/password authentication over HTTPS. Disable Disable the SAML requested authentication context. Set to True if you wish to configure the IDP to use specific authentication contexts, without the need to send one in the request. Comparison type Specifies the comparison method used to evaluate the requested authentication context. One of: "exact", "minimum", "maximum", "better".
The industry default is "exact", other options are "minimum", "maximum" and "better".
- Exact: The authn context in the assertion MUST exactly match the full expected context specified on the SP.
- Minimum: The authn context in the assertion MUST be at least as strong as one of the contexts specified on the SP.
- Better: The authn context in the assertion MUST be stronger than any of the contexts specified on the SP.
- Maximum: The authn context in the assertion MUST be as strong as possible for all of the contexts specified on the SP, without exceeding the strength of at least one context.
For more details, see the SAML 2.0 specification (Section 3.3.2.2.1).
Reference list All SAML authentication classes to be sent in the SAML authentication request. Use to tune the authentication context on the IDP side. Default="urn:oasis:names:tc:SAML:2.0:ac:classes:PasswordProtectedTransport" (Which means user/password over HTTPS). For more details, see the SAML 2.0 specification (Section 3.3.2.2.1 & Section 2.7.2.2). Declaration list All SAML authentication declarative classes to be sent in the SAML authentication request. For details, see the SAML 2.0 specification (Section 3.3.2.2.1 & Section 2.7.2.2). Signout The sign-out redirection settings. Override signout URL Enable this option to redirect to another page than the default sign-out page. The default page when you sign out is the Collibra Console sign-in page. Signout redirect URL The URL to redirect to when you sign out. - Click Save all.