The MicroStrategy integration supports both MicroStrategy Cloud and MicroStrategy on-premises environments. Before you start the integration, you have to enable Collibra to access your MicroStrategy data.
Requirements and permissions
The following permissions apply only to MicroStrategy on-premises customers.
-
You need Admin API permissions.
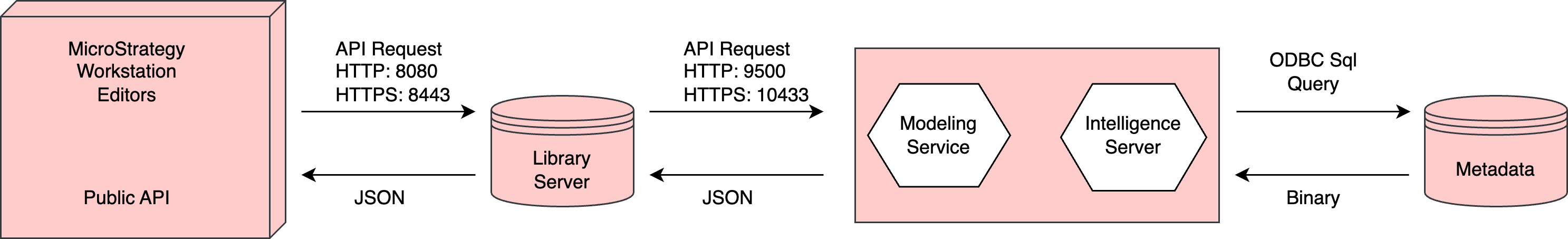
The first call we make to MicroStrategy is to authenticate. We connect to <MSTR URL>:<Port>/MicroStrategyLibrary/api-docs/ and use POST api/auth/login. You have to ensure that this API call can be made successfully. - You need permissions to access the library server.
- The lineage harvester uses port 443. If the port is not open, you also need permissions to access the repository.
- If you have a MicroStrategy on-premises environment, you need the permissions for all of the database objects that the lineage harvester accesses.
- You have to configure the MicroStrategy Modeling Service. For complete information, see the MicroStrategy documentation.
- Necessary permissions to all database objects that the lineage harvester accesses.Show me the data source-specific permissions
Data source
Required permissions
Amazon Redshift
You need read access on information_schema. Only views that you own are processed.Azure Data Factory
Ensure that you meet the Azure Data Factory-specific permissions described in Set up Azure Data Factory.Azure SQL server
You need read access on the SYS schema.Azure Synapse Analytics
SELECT, at table level. Grant this to every table for which you want to create a technical lineage.Google BigQuery
You need read access on information_schema:- bigquery.datasets.get
- bigquery.tables.get
- bigquery.tables.list
- bigquery.jobs.create
- bigquery.routines.get
- bigquery.routines.list
Greenplum
A role with the LOGIN option.HiveQL
SELECT WITH GRANT OPTION, at Table level.IBM DB2
CONNECT ON DATABASEInformatica Intelligent Cloud Services
- Your user role must have privileges to export assets.
- You must have read permission on all assets that you want to export.
Matillion
- You have at least a Matillion Enterprise license.
- You have generated the Matillion certificate. For more information, go to Recreating self-signed SSL certificates on a Matillion ETL instance.
- You have added the Matillion certificate to a Java truststore. For more information about adding a certificate to a Java truststore, go to Add a Certificate to a Truststore Using Keytool.
Microsoft SQL Server
You need read access on the SYS schema and the View Definition Permission in your SQL Server.MySQL
SELECT, at table level. Grant this to every table for which you want to create a technical lineage.Netezza
You need read access on definition_schema.Oracle You need read access to the following dictionary views:- all_tab_cols
- all_col_comments
- all_objects
- ALL_DB_LINKS
- all_mviews
- all_source
- all_synonyms
- all_views
PostgreSQL
- GRANT SELECT, at table level. Grant this to every table for which you want to create a technical lineage.
-
The role of the user that you specify in the
usernameproperty in lineage harvester configuration file must be the owner of the views in PostgreSQL.
Snowflake The following permissions are required, regardless of the ingestion mode:SQLorSQL-API.You need a role that can access the Snowflake shared read-only database. To access the shared database, the account administrator must grant the IMPORTED PRIVILEGES privilege on the shared database to the user that runs the lineage harvester.If the default role in Snowflake does not have the IMPORTED PRIVILEGES privilege, you can use thecustomConnectionPropertiesproperty in the lineage harvester configuration file to assign the appropriate role to the user. For example:"customConnectionProperties": "role=METADATA"Teradata
You need read access on the DBC.
Important To access MicroStrategy data, you have to use the In-memory Dataset connection method in MicroStrategy, not the Live Connect connection method. If the data is not stored in memory, the MicroStrategy APIs can't access it.
Using a proxy server
If you are using a proxy server, confirm with your Collibra Admin that your proxy server is configured to access the library server.
Using a custom URL to connect to the MicroStrategy Library Server
Important This requirement applies only if you are connecting to a proxy server.
If you are using a custom URL to connect to the MicroStrategyLibrary Server, you have to specify the URL.
If you are creating a technical lineage:
- Via Edge, specify the URL in the MicroStrategy Library URL field, in yourEdge capability.
- Via the lineage harvester, use the
microStrategyLibraryUrlproperty in your lineage harvester configuration file, to specify the URL.