As a BI Admin, register Power BI in Microsoft Azure and set the necessary permissions before you start the technical lineage process. This configuration enables Edge or the lineage harvester (deprecated) to connect to Power BI and harvest metadata.
Be sure to read about the supported authentication methods before you register Power BI in Microsoft Azure.
Warning This procedure is performed outside of Collibra. We highly recommend that you carefully read the source documentation.
Steps
- Follow the instructions in the Microsoft Azure documentation to register Power BI in the Azure Portal using the following settings:
Setting
Description
Name The name of your Power BI application. Supported account types The type of tenant. This indicates who can access the Power BI application.
In this case, the supported account type must be Single tenant.
Redirect URI The location to which a user's client is redirected and where security tokens are sent after a successful authorization.
In this case, the redirected URI must be Web, but you do not have to specify any web location.
When you have registered Power BI, the Azure portal creates two important IDs that you need:- The Application (client) ID
- The Directory (tenant) ID
Store these IDs for future reference. You can find the IDs in the Overview pane on the Azure portal or in the top right menu. - Go to the API permissions pane and do the following:
- Select Delegated permissions as permission type.
- Grant the Power BI application in Microsoft Azure the Microsoft Graph
User.Readpermission.
The user now has the following permissions:- Microsoft Graph
User.Read
Important You cannot have any API permissions with Admin consent set to Yes.
- In the Power BI Admin portal, do the following:
- Enable the Allow service principals to use read-only admin APIs option.
- Enable the Enhance admin APIs responses with detailed metadata option.
- Enable the Enhance admin APIs responses with DAX and mashup expressions option.
- Apply the option to specific security groups.
- Enter the name of the security group to which you want to add the service principal.
Warning The Power BI APIs do not support mail-enabled security groups.Note You need Power BI administrator rights to access the Power BI Admin portal.
Steps
-
Follow the instructions in the Microsoft Azure documentation to register Power BI in the Azure Portal using the following settings:
Setting
Description
Name The name of your Power BI application. Supported account types The type of tenant. This indicates who can access the Power BI application.
In this case, the supported account type must be Single tenant.
Redirect URI The location to which a user's client is redirected and where security tokens are sent after a successful authorization.
In this case, the redirected URI must be Web, but you do not have to specify any web location.
When you have registered Power BI, the Azure portal creates two important IDs that you need:- The Application (client) ID
- The Directory (tenant) ID
Store these IDs for future reference. You can find the IDs in the Overview pane on the Azure portal or in the top right menu. - Create a user with the Power BI Administrator role.
- The user must have administrator rights (such as Office 365 Global Administrator or Power BI Service Administrator) in Power BI.
- Delegated permissions are supported.
- In the Azure portal, go to the Authentication pane and do the following:
- Go to the Advanced settings section.
- Set the Treat application as a public client to Yes.Note When Power BI is registered in Microsoft Azure, the Treat application as a public client setting label changes to Allow public client flows.
- Go to the API permissions pane and do the following:
- Select Delegated permissions as permission type.
- Grant the Power BI application in Microsoft Azure the Microsoft Graph
User.Readpermission. - Grant the Power BI application in Microsoft Azure all Power BI Service permissions.
- Set Admin consent required for
Tenant.ReadAllpermission to Yes.Note Also ensure that the user who runs the lineage harvester has been granted the Admin consent.
The user now has the following permissions:- Microsoft Graph
User.Read
- Power BI Service
App.Read.AllCapacity.Read.AllDashboard.Read.AllDataflow.Read.AllGroup.Read.AllReport.Read.AllWorkspace.Read.AllTenant.Read.All: You need explicit Admin consent. If you have explicit Admin consent, "granted for" is shown in the Status column.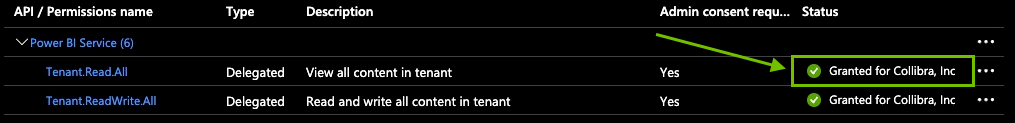
- In the Power BI Admin portal, do the following:
- Enable the Enhance admin APIs responses with detailed metadata option.
- Enable the Enhance admin APIs responses with DAX and mashup expressions option.
Apply the integration setting to the entire organization (default) or to the specific security group to which your workspaces belong.