To ensure successful metadata ingestion and lineage generation, complete the following preflight checks.
In your MicroStrategy environment
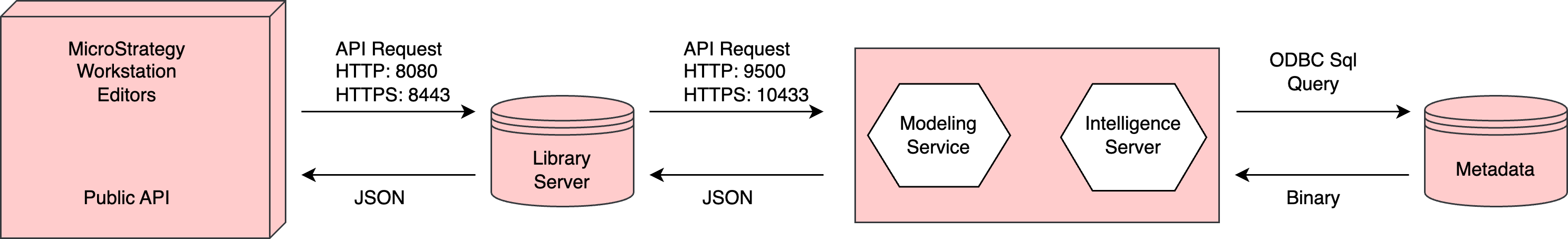
The integration uses a set of specific API calls to communicate with the MicroStrategy Library. During the process, the integration loads all required cookies and maintains the session to ensure a complete metadata harvest from both in-memory and live-connect datasets.
-
You need the following Admin API permissions:
- The first call we make to MicroStrategy is to authenticate. We connect to:
<MSTR URL>:<Port>/MicroStrategyLibrary/api-docs/ and use GET api/auth/login.
For complete information, see the MicroStrategy documentation.
If this API call can be made successfully, you can ingest the metadata. - The same connection:
<MSTR URL>:<Port>/MicroStrategyLibrary/api-docs/, but with GET api/model/tables/<tableId>.
For complete information, see the MicroStrategy documentation.
This endpoint is needed to create lineage and stitching.
- The first call we make to MicroStrategy is to authenticate. We connect to:
- You need permissions to access the library server.
- The lineage harvester (deprecated) uses port 443. If the port is not open, you also need permissions to access the repository.
- You have to configure the MicroStrategy Modeling Service. For complete information, see the MicroStrategy documentation.
Important To access MicroStrategy data, you have to use the In-memory Dataset connection method in MicroStrategy, not the Live Connect connection method. If the data is not stored in memory, the MicroStrategy APIs can't access it.
Note Freeform SQL is supported for reports (not cubes or dossiers) if you have MicroStrategy update10 or newer, or MicroStrategy ONE.
Using a proxy server
If you are using a proxy server, confirm with your CPSH Admin that your proxy server is configured to access the library server.
Using a custom URL to connect to the MicroStrategy Library Server
Important This requirement applies only if you are connecting to a proxy server.
If you're using a custom URL to connect to the MicroStrategy Library Server, you have to specify the URL. Specify the URL in the MicroStrategy Library URL field, in your Edge capability.
In your CPSH environment
Lineage enablement
- Technical lineage via Edge is enabled in your CPSH environment.
Edge
-
You created and installed an Edge site.Important If you're using a Collibra Cloud site, go the Collibra Cloud site documentation to check if your data source is supported.
- The Edge site status must be Healthy.
Network and proxy configuration
- Edge can connect to all Collibra Data Lineage service instances in your geographic location.
- Optionally, you've connected to a proxy server.
- Optionally, use a custom certificate to allow the Edge capability to connect to your data source. In this case, you've saved the certificate as "ca.pem" in the same directory as the Edge site installer. If you've saved the certificate in another directory, use the
--caargument in the Edge site installation command.
CPSH permissions
You can connect to Collibra Data Lineage by using the basic or OAuth authentication method. The following permissions are required only if you use the basic authentication method.
- A global role with the following global permissions:
- Data Stewardship Manager
- Manage all resources
- System administration
- Technical lineage
- A resource role with the following resource permissions on the community level in which you created the domain:
- Asset > Add
- Attribute > Add
- Domain > Add
- Attachment > Add
To create a new target domain for asset ingestion:
- You have a resource role with the Domain > Add resource permission.
To create a MicroStrategy connection:
- You have a global role with the Product Rights > System administration global permission.
- You have a global role that has the Manage Edge sites global permission.
- You have a global role that has the Manage connections and capabilities global permission.
- A resource role with Configure external systemresource permission, for example Owner.
- You have added a vault to your Edge site.
- If your data source connection requires a file from your vault, the file must be encoded into Base64 and stored as a regular secret in your vault.
To connect to Collibra Data Lineage service instances via OAuth authentication:
- You have a global role with the Product Rights > System administration global permission.
- You have a global role that has the Manage Edge sites global permission.
- You have a global role that has the Manage connections and capabilities global permission.
To add an Edge capability:
- You have a global role with the Product Rights > System administration global permission.
- You have a global role that has the Manage connections and capabilities global permission, for example, Edge integration engineer.
To synchronize technical lineage:
- A global role that has the following global permission:
- Catalog, for example Catalog Author
- View Edge connections and capabilities
- A resource role with Configure external system resource permission, for example Owner.
- Data source-specific permissions.