To integrate Microsoft Fabric, set up a service principal in Microsoft Entra ID and grant the required permissions to it in Fabric.
Steps
- Register an application in Microsoft Entra ID and create a client secret.
- Complete the steps in the Register an application topic in Microsoft Entra documentation.
- Complete the steps in the create a new client secret topic.
- Grant the
Organization.Read.Allapplication permission from Microsoft Graph to the service principle created in step 1. This permission is required to read Fabric tenant information. If you are unable to provide theOrganization.Read.Allpermission to the service principal, you can instead specify the Fabric tenant name and capacity name(s) in the integration using the Custom tenant name and Custom capacity name fields.For detailed steps, go to Application permission to Microsoft Graph in Microsoft Entra documentation.
The following graphic shows how to grant the
Organization.Read.Allapplication permission.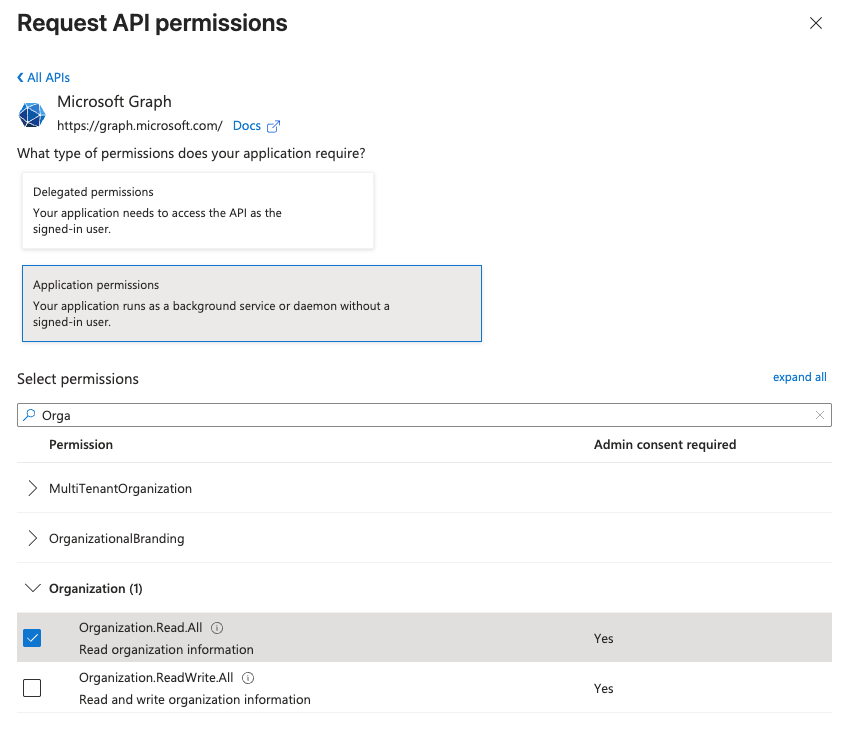
- Create a security group in Microsoft Entra ID application, and add the service principal created in step 1 as a member.
Ensure the Group type is
Security.For detailed steps, go to Manage Microsoft Entra groups and group membership in Microsoft Entra documentation.
The Microsoft Entra application ID and client secret are displayed in the Summary box.
- Associate the service principal with your Fabric tenant.
Log in to the Fabric Admin Portal as a Tenant Administrator and enable the following settings:
- Service principals can call Fabric public APIs, and select the security group created in step 3.
- Service principal authentication for admin APIs and select the security group created in step 3.
- Enhance admin APIs responses with detailed metadata.
- Assign the Viewer role in the Fabric workspace and Read access in the Fabric capacity to the service principal or security group.
For detailed steps, go to Give users access to workspaces in Microsoft Fabric documentation.
- Optionally, if you want to profile, classify data, and request sample data, grant the
db_datareaderrole to the service principal for each SQL database.The following graphic shows how to grant the
db_datareaderrole.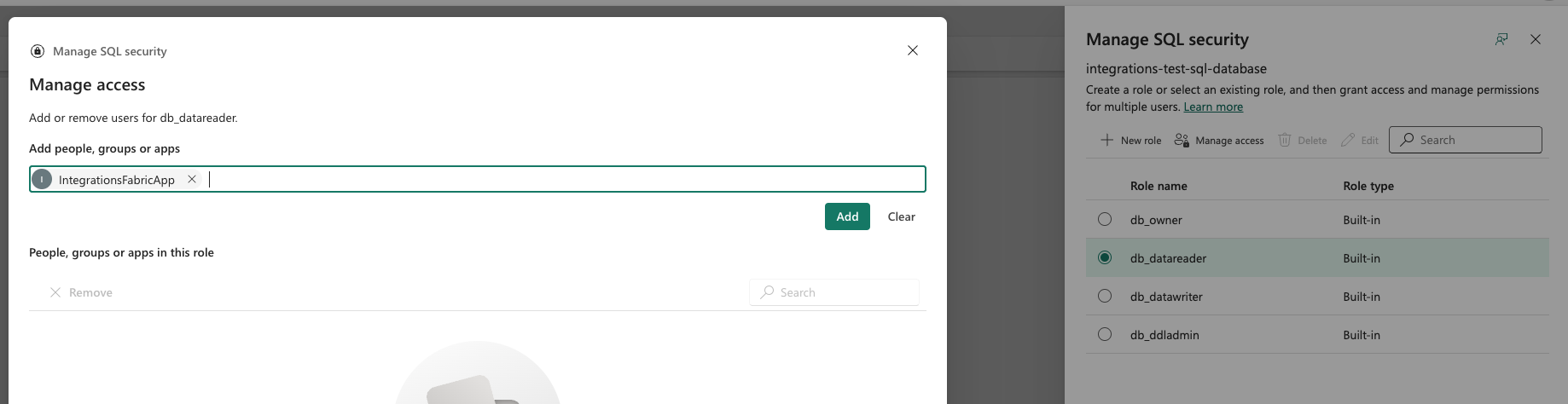
You can now Create an Azure connection to an Edge or Collibra Cloud site.