Storing secrets
Secrets for connections and capabilities are stored solely on the Edge site. While at rest, secrets are using envelope encryption where the secret is encrypted by a key, which on its turn is encrypted by another key.
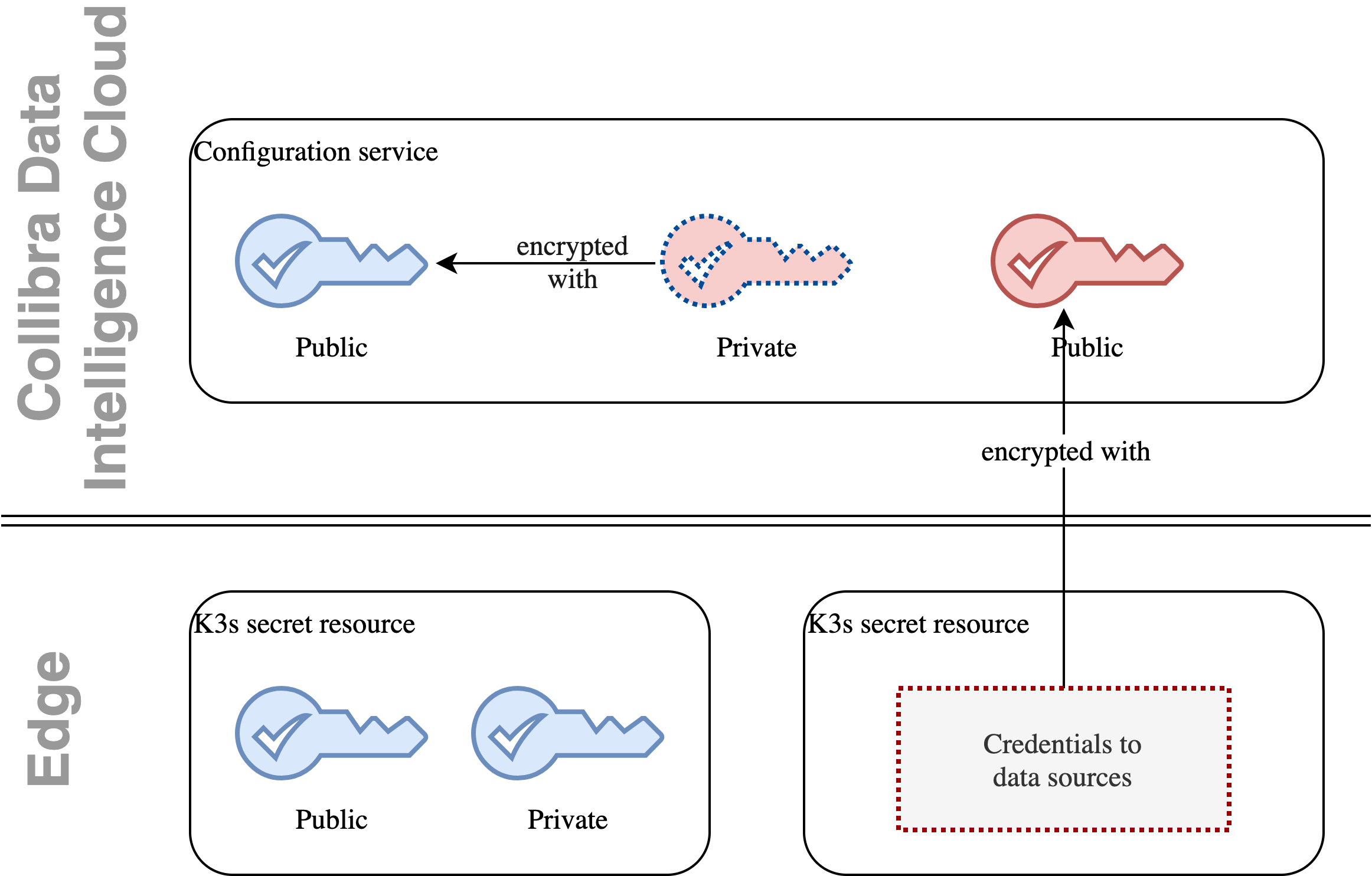
The Edge native encryption mechanism is based on two RSA key pairs. They are stored in the following places:
| Keys | DIC server | Edge server | Purpose |
|---|---|---|---|
| Public red key | Yes | No | Used to encrypt credentials |
| Private red key | Yes (encrypted using public blue key) | No | Used to decrypt credentials |
| Public blue key | Yes | Yes | Used to encrypt red private keys |
| Private blue key | No | Yes | Used to decrypt red private key |
The blue key pair is stored as a Kubernetes secret on the Edgeserver so it undergoes a native K3S encryption as described here.
An Edge site owns the Blue key pair, with the Blue private key stored on Edge. Similar to that, Collibra Data Intelligence Cloud owns the Red key pair. Every secret on Edge is encrypted with the private Red key, which is sent to the Edge site for each capability execution, encrypted with the Blue public key. Once on the Edge site, Red private key is decrypted, and secrets needed to execute a connection or a capability are decrypted and injected into the capability container.
Note Inside the k8s cluster, all other secrets, for example data source credentials and datadog credentials, are stored encrypted at rest.